Zfone, ZRTP and some rumination on PKIs and trust
March 24, 2006I like this guy! Phil Zimmermann quietly released a very neat application, Zfone as a reference application of his new cryptographic protocol ZRTP aimed to bring privacy to your VoIP calls. I hope it won’t cause him all the troubles that PGP brought him.
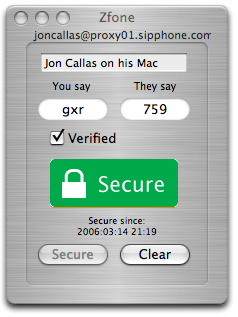
Zfone lets you whisper in someone’s ear, even if their ear is a thousand miles away. I think it’s better than the other approaches to secure VoIP, because it achieves security without reliance on a PKI, key certification, trust models, certificate authorities, or key management complexity that bedevils the email encryption world. It performs its key agreements and key management in a purely peer-to-peer manner over the RTP packet stream.
Yes, Phil! You are absolutely right! Most certification authorities have sloppy certification procedures and most user do not care to maintain a secure list of accountable authorities in their clients (e.g. browsers). Today use of public key cryptography in conjunction with PKI or trust models is objectionable and implies plenty of risks and inconveniences. From authentic but fraudulent certificates to back doors.
A decade of industry experience has shown that deploying centrally managed PKIs can be a painful and often futile experience. PKIs are just too messy, and require too much activation energy to get them started.
Public key algorithms are good, public key infrastructures are bad.
I like Zfone because, like in real world, it assumes that trust needs to be continuously renewed and updated between the two parties.
It uses ephemeral Diffie-Hellman (DH) with hash commitment, and allows the detection of Man in the Middle (MitM) attacks by displaying a short authentication string for the users to read and compare over the phone.
Moving from secure VoIP calls to more general application of public key cryptography, I’m asking myself a questions:
Do I feel more comfortable entering my credit card data on an ecommerce site because of the yellow lock and the Verisign certificate or because the site just proved to know me well and from a long time showing my purchase history and making some interesting personalized recommendations?
mmm …
UPDATE - Bruce Schneier just posted a very interesting essay about VoIP encryption.
No amount of IP telephony encryption can prevent a Trojan or worm on your computer – or just a hacker who managed to get access to your machine – from eavesdropping on your phone calls, just as no amount of SSL or e-mail encryption can prevent a Trojan on your computer from eavesdropping – or even modifying – your data.
So, as always, it boils down to this: We need secure computers and secure operating systems even more than we need secure transmission.
 Mastodon
Mastodon GitHub
GitHub Twitter
Twitter Google
forum
Google
forum